ABSTRACT
The investigator and prosecutor encounter enormous difficulties and challenges in dealing with the cross-border cyber related crimes. This article intends to show practical difficulties prosecutors and investigators often face when they deal with the cross-border cybercrimes. For example, foreign States often refused to share the information and evidences if the alleged conduct is not amounted to crime under their law. Further, the investigators follow the Mutual Legal Assistance Treaties (MLAT) mechanisms to request assistance and other evidences from a foreign country, which often proved to be time-consuming. Alarmingly, it became very challenging for investigators and prosecutors to identify and locate the actual perpetrator since perpetrators now use modern technologies and methods to hide their identity and location. Thus, this article aims to explore some of the common challenges prosecutors and investigators meets in their day-to-day work.
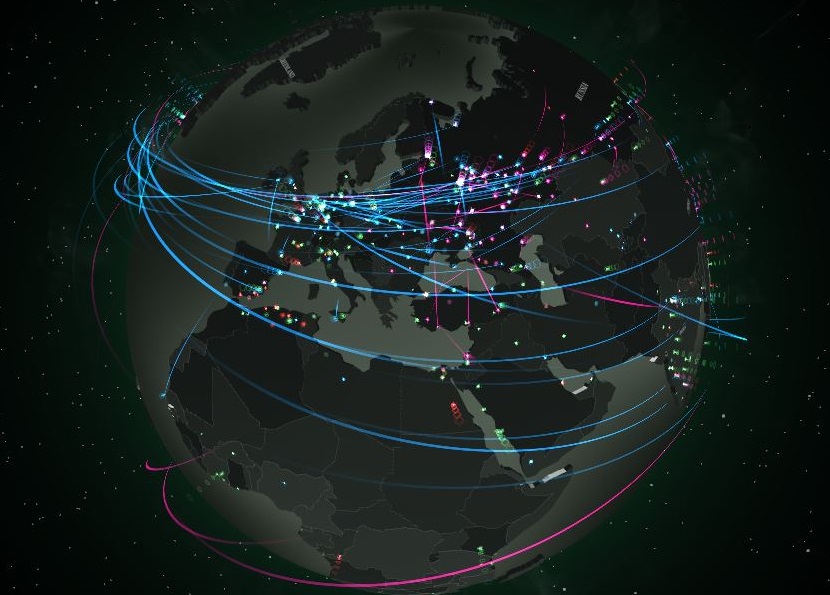
THE global nature of the internet creates serious problems in reality. The investigators and prosecutors encounter enormous difficulties and challenges in dealing with the cross-border cyber related cases. This article intends to show practical difficulties prosecutors and investigators often face when they deal with the cross-border cybercrimes.
Differences in the legality of the Subject matter:
One of the issues which create a serious problem for the prosecutor and the investigator is differences in the legality of the subject matter. This means what is illegal under the laws of Bangladesh could be legal in other country. In today’s world it became very easy for someone sitting in nation ‘X’ to commit a criminal act against a victim physically situated within the territory of nation ‘Y’ without ever leaving his own country.[1]
This could be well explained from an earlier example where a German website was selling child pornographic contents in their website. In Germany it was legal since their age limit for entering into such business was only 14 years. However, these pornographic contents were alleged for breach of Belgian and the laws of Singapore. The website owners were indicted in Singapore because of spreading pornographic material in Singapore, even though the company has never done any business with someone from Singapore. Further, the Website owners were also ordered to appear in the Court of Belgium. This is all because some of the adult pictures were considered to be of 17 year old minors constituting the crime of child pornography under the Belgian and the laws of Singapore. This example clearly shows how a legal business under the law of Germany confronted criminal laws of all countries connected to the internet.[2]
In such situation, prosecutors encounter serious difficulties in preparing their case. For instance, they hardly find any help from the foreign investigative agencies since some countries only offer help if the conduct is illegal in the country whose assistance is being requested. Therefore, the prosecutors face unexplainable difficulties in establishing their case against the perpetrators from another jurisdiction. This is a hurdle in the investigatory process as well. This is because some countries only grant assistance if the conduct is illegal under their own law.[3]
Establishing Jurisdiction:
As an example, in a number of offences the UK legislations provide the UK to exercise its jurisdiction over an offence committed or operated extra-territorially i.e. outside the UK. For example, the Computer Misuse Act (1990) (CMA) is the main piece of UK legislation relating to offences or attacks against computer systems such as hacking or denial of service. This Act provides jurisdiction to prosecute where there is a “significant link” with the domestic jurisdiction. This usually includes the fact that the accused or the targeted computer was in England and Wales. This is not as straight forward as it sounds. The prosecutors need to find available credible evidences to establish such link. The Court often consider whether the alleged conduct or crime have a “substantial connection with the jurisdiction”. It follows that, where a substantial number of the activities constituting a crime take place within England and Wales, the Courts of England and Wales have jurisdiction unless it can be argued on a reasonable view that the conduct ought to be dealt with by the Courts of another country; (R v Smith (Wallace Duncan) (No.4) [2004] 3 WLR 229, per Lord Chief Justice Woolf).[4
In the case of R v Sheppard and Whittle (2010)[5] Sheppard posted racially inflammatory material to a website, registered in his name and operated by him, but based in California. Once the material reached the server in California, it was posted online and made available on the internet to all those visiting the website, including people in the jurisdiction of England and Wales. In this case, the Court came to the conclusion that the jurisdiction was governed by the “substantial measure principle” enunciated by the Court in R v Smith. Thus, the prosecutors need to establish “substantial connection with the jurisdiction” to invite the Court to act extra-territorially.
In some widespread cases, too many countries show their interest to investigate and prosecute a perpetrator.[6] In such situations, investigators and prosecutors often meet to decide what they should do. To resolve such issues, they need to negotiate with the investigators from other jurisdictions and need to set out how jurisdiction could be best determined. On the other hand, at times the problem of “negative international jurisdiction” also arises. This essentially means that, some cases are not investigated because they could be prosecuted in one of many countries. However, ultimately, no state authority in fact takes the action to prosecute.
Further, if an offence committed in various countries or where the offender and victim are located in different places, question arises as to which Court should deal with the matter. If the offence in question can be charged in the country in which the offender is located then problems of extradition will be avoided. However, if the offence must be charged in the country in which the victim is located or where the effect of the conduct occurred, then the offender will need to be extradited to that country. This often creates problem for the investigators and prosecutors if the states do not have extradition treaty. At times, prosecutors need to initiate the case in absentia i.e. trial in absence of alleged perpetrator. For instance, in May 2014, five Public Liberation Army officers (member of an organization based on Shanghai, China) were charged in absentia by US authorities with offences related to cyber related crime; (United States District Courts, USA v Wang [2014] 944 F.2d 80).
Collecting Evidence:
The recent intensification of the cybercrime is alarming. However, prosecutors and other investigator authorities face enormous problems in collecting evidences to prosecute the perpetrators operating criminal conduct extra-territorially. In an international context, it is often difficult and time-consuming to establish which jurisdiction regulates the preservation and collection of evidence from online service providers. Further, it has been analysed that the number of unreported online victims are “higher than in the physical world”.[7] This means the prosecution team do not receive enough evidence to overcome the evidential threshold to initiate the case against the perpetrator. Even if they receive the statements from the victims, however they often fail to detect the perpetrators. The investigators often rely on the international cyber related agencies to obtain the evidence. This is because the state investigatory agencies cannot directly enter into another State’s jurisdiction to obtain information and evidences. They need to negotiate with other agencies to use mutual legal assistance (MLA) channels.
At times this negotiation process wholly depends on the political relationship between the States. It also shows that, different countries have different priorities and focus areas in terms of the importance of cybercrime investigations. In majority countries, economic crimes committed using computers are often at the bottom of the hierarchy of importance in countries where violent crime is prevalent, or where national security interests may be at stake. As a consequence, the requests for assistance in cybercrime cases may simply be given a much lower priority, especially if they have come from a country with no history of cooperative action.[8]
Moreover, under the Mutual Legal Assistance Treaties (MLAT), prosecutors in one country may request assistance from their counterparts in a foreign country in order to perform tasks including the investigation of suspects and the collection of evidence.[9] Once provided by the foreign counterpart, the collected evidence may be used in a prosecution in the requesting country. While simple in concept, the MLAT process is often difficult and time-consuming to accomplish. The detailed nature of the request and the requirement for international approval can often complicate and impede efforts at information gathering.[10]
State Sponsored Cybercrime:
It is already established by a number of researches that the States and States-sponsored agents often engage in cybercrime. For instance, there are number of allegations have been made that the Chinese authorities are engaged in wide-spread economic and industrial espionage, and the US Government has engaged in massive programs of cyber-surveillance.[11] These State sponsored actions may not be defined as criminal act under the laws of the State that undertakes them, but are usually regarded as crimes by the State that is on the receiving end. Yet, prosecutors and investigators can do very little in such cases even if they produce very strong evidence in supporting such cyber-attack against a State
For example, in 2014, allegations have been made that the North Korea sponsored a hack on Sony Pictures Entertainment, US. It was concluded by the US intelligence officials that the hack was originated in North Korea, and may have been sponsored by the North Korean government. The North Korean government not only denied the involvement but refused to provide any assistance to international prosecution efforts.[12] This outcome is plainly evident that, without the cooperation of other State there is simply no mechanism for foreign governments to take effective legal action against the individuals who perpetrated the act.
Securing Extradition: “Dual Criminality”
Securing extradition is one of the most challenging stages for the investigator and prosecution team. Extradition requires not only that an appropriate treaty exist between the two countries concerned, but also that the conduct in question be criminalised in both referring and receiving country i.e. “dual criminality”. In the case of cyber related crime, this is often not the case.
An example of the kind of difficulties that can arise concerns the case of “Onel de Guzman” who was alleged to have sent out the so-called “Love Bug virus” in May 2000. The virus which infected Microsoft Windows operating systems was sent by E-mail attachments which when opened damaged files in the computer and then replicated itself by sending similar messages to all the addresses in the infected computer’s address book. The estimated damage caused globally was estimated to be between $6.7 billion and $15.3 billion. The virus was traced to an internet service provider in the Philippines who cooperated with police to locate the residence in question. A computer science student named Onel de Guzman was arrested but the creation and release of a computer virus was not illegal by Philippine law at that time. Since the conduct was not illegal in the Philippines he could not be extradited to the US where the conduct was illegal. This was due to the principle of “dual criminality”.[13]
Hard to detect and find identity:
The investigators and prosecutors encounter serious difficulty in establishing the identity and responsibility of a particular crime took place in cyber-world.[14] For example, one may hack X’s face-book account from outside of Bangladesh and use his account to commit a crime. Thus, at the initial stage, the face-book account holder would be accountable for the crime committed by someone else.
For instance, in March 2003, a case was reported in the UK that provides a good example of the problem of trans-national identity related fraud. The case concerned a 72 year-old man, Derek Lloyd Sykes, whom the FBI was investigating in connection with alleged cyber telemarketing fraud involving millions of dollars in the US. Since 1989, Derek Sykes had been making use of the identity of a 72-year old retired businessman from Bristol in the UK, Derek Bond, who had never met Derek Sykes, and had no connection with his alleged crimes at all. The FBI issued a warrant for the arrest of Derek Sykes and this was executed by South African Police in Durban on 6 February 2003 in the name of Derek Bond. Unfortunately, Derek Bond, the retired businessman, who was on holiday with his wife, was arrested instead of Derek Sykes. Mr Bond was held in custody at police headquarters in Durban until 26 February 2003 when he was released following the arrest of the real suspect, Derek Sykes.[15]
Further, criminals can use sophisticated methods to hide their identity and location. In this regard, recent joint report of Eurojust and Europol states that the increasing criminal use of “encryption”, “anonymisation” tools, “virtual currencies” and the “Darknets” have led to a situation where law enforcement may no longer (reasonably) establish the physical location of the perpetrator, the criminal infrastructure or electronic evidence.[16] In these situations, it is often unclear which country has jurisdiction and what legal framework regulates the collection of evidence or the use of special investigative powers such as monitoring of criminal activities online and various undercover measures.
In recent time, perpetrators are taking the help of new technologies to commit crimes. Therefore, it is really becoming tough for the prosecutors and investigators to locate the perpetrator, understand the issue, and establish the case against the actual perpetrators. It even becomes more challenging when investigators cannot directly conduct the investigation and rely on the information provided by other foreign agencies. Therefore, this area should be explored further and States should sit together and take initiatives to conduct in-depth research work to harmonise the existing cyber-related laws. The States may consider inaugurating an all-inclusive international treaty to deal with these challenges.
_____________________________________________ [1] D. Marc Goodman and W. Brenner Susan, ‘The Emerging Consensus on Criminal Conduct in Cyberspace’ (2002) vol. 3, Journal of Law & Technology, pp 4-24. [2] Susan W. Brenner and Bert-Jaap Koops, ‘Approaches to Cybercrime Jurisdiction’ (2004) vol. 4 J. High Tech. L. 1 at page 3. [3] Ibid. [4] See also: Jurisdiction, Legal Guidance: Crown Prosecution Service. Available at: <http://www.cps.gov.uk/legal/h_to_k/jurisdiction/> Last Accessed on 11th July 2017. [5] R v Sheppard and Whittle (2010) EWCA Crim 65. [6] Dr Russell and G. Smith, Investigating Cybercrime: Barriers and Solutions (Pacific Rim Fraud Conference Sydney, 11 September 2003). Available at: <http://www.aic.gov.au/media_library/conferences/other/smith_russell/2003-09-cybercrime.pdf> Last Accessed on 11th July 2017. [7] Jo Bryce, ‘Online sexual exploitation of children and young people’ in Yvonne Jewkes and Majid Yar (eds), Handbook of Internet Crime (Willan Publishing, 2010) at page. 322. [8] Dr Russell and G. Smith (n 6). [9] T. Marcus Funk, Mutual Legal Assistance Treaties and Letters Rogatory: A Guide for Judges (Federal Judicial Center, 2014) at page 2-3. [10] Ibid. [11] Roderic Broadhurst, Peter Grabosky, Mamoun Alazab & Steve Chon, ‘Organizations and Cyber crime: An Analysis of the Nature of Groups engaged in Cyber Crime’ (2014) Vol. 8:1, International Journal of Cyber Criminology, pp. 1–20. [12] David E. Sanger and Nicole Perlrothdec, U.S. Said to Find North Korea Ordered Cyberattack on Sony, (2014). Available at: <https://www.nytimes.com/2014/12/18/world/asia/us-links-north-korea-to-sony-hacking.html> Last Accessed on 2nd of July 2017. [13]R. E. Bell, ‘The Prosecution of Computer Crime’ (2002) vol. 9:4, Journal of Financial Crime, pp. 308-25. [14] R. Broadhurst & P. Grabosky, ‘Computer-Related Crime in Asia: Emergent Issues’ in R. Broadhurst & P. Grabosky (Eds.), Cyber-crime: The Challenge in Asia (Hong Kong: Hong Kong University Press) at pp. 347–360. [15] BBC News, Pensioner freed after FBI bungle (26 February, 2003). Available at: <http://news.bbc.co.uk/1/hi/england/2799791.stm> Last Accessed on 22nd June 2017. See also: BBC News, How the mix-up happened (26 February, 2003). Available at: <http://news.bbc.co.uk/1/hi/england/2799929.stm> Last Accessed on 22nd June 2017. [16] Eurojust and Europol, Common challenges in combating cybercrime (Brussels, 13 March 2017, 7021/17).
Leave a Reply